Cisco Asa Keygen
Managing Licenses with Activation KeysAn activation key is an encoded bit string that defines the list of features to enable, how long the key would stay valid upon activation, and the specific serial number of a Cisco ASA device. A series of five hexadecimal numbers, as shown at the top of the output in Example 3-1, typically represents that string.
Cisco asa 5505 keygen. How to make a christmas cracker costume. 5 Create your private and public key. How to Activate Key ASA. Skip navigation Sign in. This video is unavailable. Cisco ASA Training 101 - Duration: 15:42. Soundtraining.net 249,117 views. It was not very clear to me but now I understand why there is no windows version of this script. You need to run it from the shell of your GNSVM and not from your main operating system.
Each activation key is only valid for the particular hardware platform with the specific encoded serial number. The complete set of activation keys resides in a hidden partition of the built-in flash device of a Cisco ASA; other nonvolatile internal memory structures maintain a backup copy of that information. After Cisco generates a key for a given device, you cannot separate individual features from this licensed package.
You can request and apply another key with a different set of features to the same Cisco ASA device at any future point in time. All features encoded in a particular key always have the same licensed duration, so activation keys can be classified as permanent or time-based.
Permanent and Time-Based Activation KeysEvery Cisco ASA model comes with a certain set of basic features and capacities enabled by default; the Base License permanently activates these features on the particular platform. Even though these core features do not require an explicit activation key, one usually comes installed anyway. This is the permanent activation key, which never expires.
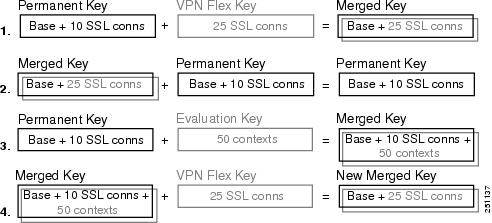
Although the system does not require this key for basic operation, some advanced features, such as failover, depend on the permanent activation key in order to operate correctly. You can enable additional features without a time limit by applying a different permanent activation key. Because a Cisco ASA device can have only one permanent activation key installed at any given time, every new key must encompass the entire set of desired features.
The feature set enabled by the new permanent activation key completely replaces the previously enabled permanent feature set, instead of merging with it. In rare situations in which the permanent activation key becomes lost or corrupted, the output of the show activation-key command displays the following value: Running Permanent Activation Key: 0x00000000 0x00000000 0x00000000 0x00000000If this happens, the system continues to operate with the default set of basic features for the platform. Reinstall the permanent activation key to restore the desired feature set. Although you can always obtain the replacement key from Cisco, it is a best practice to always maintain a backup of all activation keys used by your Cisco ASA devices.In addition to the permanent activation key, you can install one or more time-based keys to enable certain features for a limited period of time.
All premium features can be activated by either permanent or time-based keys, with the exception of Botnet Traffic Filter, which is only available via a time-based license. Even though you can apply multiple time-based activation keys on the same Cisco ASA concurrently, only one license remains active for any particular feature at any given time. Thus, several time-based keys can stay active on the ASA as long as they enable different features.
Other time-based keys remain installed but inactive until needed. Only the currently active licenses for each feature continue the time countdown; you can stop the timer by manually deactivating a key or installing a different time-based license for the same feature.
In Cisco ASA Software version 8.3(1) and later, time-based key expiration no longer depends on the configured system time and date; the countdown occurs automatically based on the actual uptime of the ASA. Combining KeysEven though only one time-based activation key can be active for any particular feature at any given time, two identical time-based keys will license a feature for the combined duration. All of the following conditions must be satisfied for this to happen:. Both current and new time-based keys enable only one feature.
Typically, this is how you receive all time-based activation keys from Cisco. Both keys license the feature at exactly the same level.
If the feature is tiered, the licensed capacities have to match.For example, assume that you have a Cisco ASA 5555-X with an active time-based key that enables 1000 AnyConnect Premium Peers for six weeks. If you add another time-based key for 1000 AnyConnect Premium Peers that has a duration of eight weeks, the new key will have the combined duration of 14 weeks.
However, the new key will deactivate the original time-based license if it enables 2500 AnyConnect Premium Peers instead or also adds the Intercompany Media Engine feature. If you install another time-based key for the IPS Module feature on the same device, both keys will activate concurrently because they enable different features. To ease the management of time-based licenses and receive the maximum advantage of combining their duration when possible, always make sure to use separate time-based activation keys for each feature and tiered capacity.When activated on the same device, the features and capacities of the permanent and active time-based keys also combine to form a single feature set, as such:. The system chooses the better value between the two key types for any feature that can be either enabled or disabled. For example, the ASA enables the Intercompany Media Engine feature based on the permanent key even if all active time-based keys have this feature disabled. For AnyConnect Premium Sessions and AnyConnect Essentials licenses that are tiered, the system picks the highest session count between the active time-based and permanent keys.
Total UC Proxy and Security Contexts counts combine between the permanent and active time-based keys up to the platform limit. This way, you can configure a total of 22 virtual contexts by adding a time-based license for 20 contexts to a Cisco ASA 5515-X with the permanent Base License for 2 contexts.Example 3-1 illustrates a Cisco ASA that derives its feature set from the permanent and one time-based activation keys. Both activation keys appear at the top of the output. Features denoted as perpetual come from the permanent activation key; these licenses never expire.

Time-based features show the remaining number of days before expiration; even if you enable one of these features via the permanent key later on, the countdown will continue until the applicable time-based key expires or becomes deactivated manually. Time-Based Key ExpirationWhen a time-base key is within 30 days of expiration, ASA generates daily system log messages to alert you of that fact. The following message includes the specific time-based activation key that is about to expire:%ASA-4-444005: Timebased license key 0x8c9911ff 0x715d6ce9 0x590258cb0xc74c922b 0x17fc9a will expire in 29 days.When the active time-based license expires, a Cisco ASA looks for another available time-based activation key that you previously installed. The system picks the next key according to internal software rules, so a particular order is not guaranteed.
You can manually activate a specific time-based key at any given time; after you do so, the deactivated time-based key remains installed with the unused licensed time still available. When all time-based keys for a particular feature expire, the device falls back to using the value in the permanent key for this feature.
Upon any expiration event, an ASA generates another system log message that lists the expired key and the succession path for the license. The following message shows that the states of all licensed features from the expired time-based key reverted to the permanent key:%ASA-2-444004: Timebased activation key 0x8c9911ff 0x715d6ce9 0x590258cb0xc74c922b 0x17fc9a has expired. Applying permanent activation key 0x725e3a190xe451697e 0xcd509dd4 0xeea888f4 0x1bc79c.As time-based licenses expire, certain features may deactivate completely and some licensed capacities of other features may reduce. Although these changes typically do not affect existing connections that are using a previously licensed feature, new connections will see the impact. For instance, assume that a Cisco ASA 5545-X appliance has the permanent activation key for 100 AnyConnect Premium Peers and a time-based license for 1000 AnyConnect Premium Peers. If there are 250 active clientless SSL VPN peers connected when the time-based key expires, the ASA appliance will not admit any new SSL VPN users until the session count drops below 100. However, the existing user sessions would remain operational with no impact.
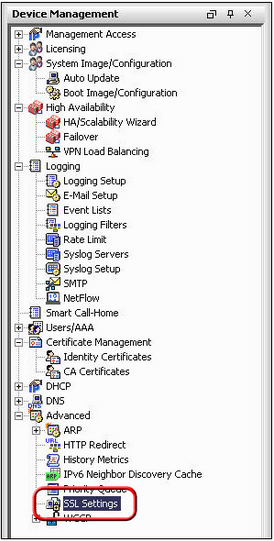
On the other hand, the Botnet Traffic Filter feature disables dynamic updates when the license expires; this removes the benefits of the feature right away.Some features may show no impact from the time-based key expiration until the Cisco ASA system reloads; because the feature is no longer licensed upon the reload, the device may reject some elements of the startup configuration. When a Cisco ASA that was previously licensed for 20 security contexts reloads with the default license, only two virtual contexts will remain operational after the system loads the startup configuration file. To avoid unexpected network outages, it is very important to monitor time-based licenses for expiration and replace them in advance; always use permanent licenses for the critical features when possible. Using Activation KeysTo apply an activation key to the Cisco ASA, you can use the activation-key command followed by the hexadecimal key value.
Both permanent and time-based keys follow the same process, and you cannot determine the key duration until you attempt to install it. Example 3-2 shows a successful attempt to activate the permanent key. Keep in mind that an ASA supports only one of such keys at any given time; the feature set of the last installed key completely overwrites the previous one. Example 3-2 Successfully Activated Permanent Key ciscoasa# activation-key 813cd670 704cde05 810195c8 e7f0d8d0 4e23f1afValidating activation key.
This may take a few minutes.Both Running and Flash permanent activation key was updated with the requested key.As shown in Example 3-3, the system specifically notes a time-based key as such during the same activation process; you can see the remaining time before expiration as well. Example 3-3 Successfully Activated Time-Based Key ciscoasa# activation-key d069a6c1 b96ac349 4d53caa7 d9c87b5Validating activation key. This may take a few minutes.The requested key is a timebased key and is activated, it has 7 days remaining.When you add a new time-based activation key that enables a single feature at the same level as another currently active key, the remaining time from the current key adds to the new key, as shown in Example 3-4. Keep in mind that both the current and new time-based keys must enable only one feature with the exact same capacity, if applicable; otherwise, the new key will deactivate and replace the current one. Example 3-4 Time-Based Activation Key Aggregation ciscoasa# activation-key fa0f53ee a906588d 5165c36f f01c24ff 0abfba9dValidating activation key.
This may take a few minutes.The requested key is a timebased key and is activated, it has 63 days remaining, including 7 days from currently active activation key.You can also deactivate a previously installed time-based license using the optional deactivate argument at the end of the activation-key key command, as shown in Example 3-5; this keyword is not available for the permanent activation key. After it is deactivated, the time-based key remains installed on the Cisco ASA. You can always reactivate this license later either manually or automatically upon the expiration of another time-based license. Example 3-5 Deactivating a Time-Based Key ciscoasa# activation-key d069a6c1 b96ac349 4d53caa7 d9c87b5 deactivateValidating activation key. This may take a few minutes.The requested key is a timebased key and is now deactivated.In rare cases, the new permanent key that disables certain features may require a reload of the system before the change occurs.
Cisco Firewall
Example 3-6 shows the warning that the system displays before the strong encryption feature gets disabled by the new permanent license. Example 3-6 Disabling a Feature with Reload Requirement ciscoasa# activation-key 6d1ff14e 5c25a1c8 556335a4 fa20ac94 4204dc81Validating activation key. This may take a few minutes.The following features available in running permanent activation key are NOTavailable in new permanent activation key:Encryption-3DES-AESWARNING: The running activation key was not updated with the requested key.Proceed with update flash activation key? confirm yThe flash permanent activation key was updated with the requested key,and will become active after the next reload.Because activation keys tie to a particular device using the serial number, it is possible to attempt to activate a key from one Cisco ASA on another; the software automatically checks for such errors and rejects an incorrect key. Example 3-7 illustrates such an attempt. Example 3-7 Invalid Activation Key Rejected ciscoasa# activation-key 350ded58 7076f6c6 01221110 c67c806c 832ccf9fValidating activation key.
This may take a few minutes.not supported yet.ERROR: The requested activation key was not saved because it is not valid for thissystem.In older Cisco ASA Software versions, it is also possible for the system to reject an activation key when it contains unknown features. In Cisco ASA 8.2(1) and later software, all keys are backward compatible regardless of whether new features are present or not. For instance, when you downgrade from Cisco ASA 9.1(2) to 9.0(2) software with the IPS Module license enabled, the same activation key remains valid after the downgrade even though the older software no longer supports this feature.
License RequirementsASA LicensesThe ASA 5508-X or ASA 5516-X includes the Base license by default, along with the Strong Encryption (3DES/AES) license if you qualify for its use. You can also purchase the following licenses:■ Security Context■ AnyConnect Plus or ApexIf you need to manually request the Strong Encryption license (which is free), see.If you want to upgrade from the Base license to the Security Plus license, or purchase an AnyConnect license, see. See also the and the. You will then receive an email with a Product Authorization Key (PAK) so you can obtain the license activation key.
For the AnyConnect licenses, you receive a multi-use PAK that you can apply to multiple ASAs that use the same pool of user sessions.Note: The serial number used for licensing is different from the chassis serial number printed on the outside of your hardware. The chassis serial number is used for technical support, but not for licensing. To view the licensing serial number, enter the show version grep Serial command or see the ASDM Configuration Device Management Licensing Activation Key page.ASA FirePOWER LicensesThe ASA FirePOWER module uses a separate licensing mechanism from the ASA. No licenses are pre-installed, but the box includes a PAK on a printout that lets you obtain a license activation key for the following licenses:■ Control and Protection —Control is also known as “Application Visibility and Control (AVC)” or “Apps”. Protection is also known as “IPS”.
In addition to the activation key for these licenses, you also need “right-to-use” subscriptions for automated updates for these features.The Control (AVC) updates are included with a Cisco support contract.The Protection (IPS) updates require you to purchase the IPS subscription from. This subscription includes entitlement to Rule, Engine, Vulnerability, and Geolocation updates.
Note: This right-to-use subscription does not generate or require a PAK/license activation key for the ASA FirePOWER module; it just provides the right to use the updates.Other licenses that you can purchase include the following:■ Advanced Malware Protection (AMP)■ URL FilteringThese licenses do generate a PAK/license activation key for the ASA FirePOWER module. See the for more information.To install the Control and Protection licenses and other optional licenses, see. Note: You must use a separate inside switch in your deployment.The default configuration enables the above network deployment with the following behavior.■ inside - outside traffic flow■ outside IP address from DHCP■ DHCP for clients on inside■ Management 1/1 belongs to the ASA FirePOWER module. The interface is Up, but otherwise unconfigured on the ASA. The ASA FirePOWER module can then use this interface to access the ASA inside network and use the inside interface as the gateway to the Internet.Note: Do not configure an IP address for this interface in the ASA configuration. Only configure an IP address in the Firepower configuration. You should consider this interface as completely separate from the ASA in terms of routing.■ ASDM access on the inside interfaceNote: If you want to deploy a separate router on the inside network, then you can route between management and inside.
In this case, you can manage both the ASA and ASA FirePOWER module on Management 1/1 with the appropriate configuration changes.Procedure. Cable the following to a Layer 2 Ethernet switch:– GigabitEthernet 1/2 interface (inside)– Management 1/1 interface (for the ASA FirePOWER module)– Your computerNote: You can connect inside and management on the same network because the management interface acts like a separate device that belongs only to the ASA FirePOWER module.2. Connect the GigabitEthernet 1/1 (outside) interface to your WAN device, for example, your cable modem.Note: If the cable modem supplies an outside IP address that is on 192.168.1.0/24, then you must change the ASA configuration to use a different IP address. Interface IP addresses, HTTPS (ASDM) access, and DHCP server settings can all be changed using the Startup Wizard.
If you change the IP address to which you are connected to ASDM, you will be disconnected when you finish the wizard. You must reconnect to the new IP address.
Launch ASDMSee the on Cisco.com for the requirements to run ASDM.Note: This procedure assumes you want to use ASDM to manage the ASA FirePOWER Module. If you want to use the FireSIGHT System, then you need to connect to the module CLI and run the setup script; see the.Procedure1. On the computer connected to the ASA, launch a web browser.2.
In the Address field, enter the following URL:. The Cisco ASDM web page appears.3. Click one of the available options: Install ASDM Launcher, Run ASDM, or Run Startup Wizard.4. Follow the onscreen instructions to launch ASDM according to the option you chose. The Cisco ASDM-IDM Launcher appears.If you click Install ASDM Launcher, in some cases you need to install an identity certificate for the ASA and a separate certificate for the ASA FirePOWER module according to.5. Leave the username and password fields empty, and click OK. The main ASDM window appears.6.
If you are prompted to provide the IP address of the installed ASA FirePOWER module, cancel out of the dialog box. You must first set the module IP address to the correct IP address using the Startup Wizard.ASDM can change the ASA FirePOWER module IP address settings over the ASA backplane; but for ASDM to then manage the module, ASDM must be able to reach the module (and its new IP address) on the Management 1/1 interface over the network. The recommended deployment allows this access because the module IP address is on the inside network. If ASDM cannot reach the module on the network after you set the IP address, then you will see an error.7.
Choose Wizards Startup Wizard.8. Configure additional ASA settings as desired, or skip screens until you reach the ASA FirePOWER Basic Configuration screen. Install the LicensesThe Control and Protection licenses are provided by default and the Product Authorization Key (PAK) is included on a printout in your box. If you ordered additional licenses, you should have PAKs for those licenses in your email.Procedure1. Obtain the License Key for your chassis by choosing Configuration ASA FirePOWER Configuration Licenses and clicking Add New License.The License Key is near the top; for example, 72:78:DA:6E:D9:93:35.2. Click Get License to launch the licensing portal. Alternatively, in your browser go to3.
Enter the PAKs separated by commas in the Get New Licenses field, and click Fulfill.4. You will be asked for the License Key and email address among other fields.5. Copy the resulting license activation key from either the website display or from the zip file attached to the licensing email that the system automatically delivers.6. Return to the ASDM Configuration ASA FirePOWER Configuration Licenses Add New License screen.7. Paste the license activation key into the License box.8. Click Verify License to ensure that you copied the text correctly, and then click Submit License after verification.9.
Click Return to License Page. Configure the ASA Security PolicyProcedure1. To send traffic to the module, choose Configuration Firewall Service Policy Rules.2.
Choose Add Add Service Policy Rule.3. Choose whether to apply the policy to a particular interface or apply it globally and click Next.4. Configure the traffic match. For example, you could match Any Traffic so that all traffic that passes your inbound access rules is redirected to the module.
Cisco Asa Keygen Download
Or, you could define stricter criteria based on ports, ACL (source and destination criteria), or an existing traffic class. The other options are less useful for this policy. After you complete the traffic class definition, click Next.5. On the Rule Actions page, click the ASA FirePOWER Inspection tab.6. Check the Enable ASA FirePOWER for this traffic flow check box.7. In the If ASA FirePOWER Card Fails area, click one of the following:– Permit traffic —Sets the ASA to allow all traffic through, uninspected, if the module is unavailable.– Close traffic —Sets the ASA to block all traffic if the module is unavailable.8.
(Optional) Check Monitor-only to send a read-only copy of traffic to the module, i.e. Passive mode.9. Click Finish and then Apply.Repeat this procedure to configure additional traffic flows as desired. Where to Go Next■ For more information about the ASA FirePOWER module and ASA operation, see the “ASA FirePOWER Module” chapter in the ASA/ASDM firewall configuration guide, or the ASDM online help. You can find links to all ASA/ASDM documentation at.■ For more information about ASA FirePOWER configuration, see the online help or the or the.Cisco and the Cisco logo are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S. And other countries. To view a list of Cisco trademarks, go to this URL:.
Cisco Asa Keygen For 55x Series
Third-party trademarks mentioned are the property of their respective owners. The use of the word partner does not imply a partnership relationship between Cisco and any other company. (1110R)© 2016 Cisco Systems, Inc. All rights reserved.